Blog
The rise of DDoS: an overview of the threat landscape
With a recent Cloudflare report revealing that DDoS attacks more than doubled in 2025, Conscia Cyber Security Specialist Peter Jones takes us through the current threat landscape, what we can expect in the future, and what we can do to protect our organisations.

For the modern connected organisation, the threat of a distributed denial-of-service (DDoS) attack is ever-present. Compared to more sophisticated nature of other attack vectors, the simplicity and high efficacy of a DDoS attack has resulted in a marked increase in occurrences over the years, to the point where today we can find its presence at every level of every sector. With a recent Cloudflare report revealing that DDoS attacks more than doubled in 2025, Conscia Cyber Security Specialist Peter Jones takes us through the current threat landscape, what we can expect in the future, and what we can do to protect our organisations.
How big is the threat from a DDoS attack, currently?
The DDoS is by no means a novel approach to the cyber attack; the underlying principle predates even the internet (with the unintentional overwhelming of ARPANET by the Morris worm in the 1980s) and by the 2010s the DDoS attack was a recognised – though still comparatively rare – threat to internet-connected organisations. Up to this point, such attacks were typically measured in the tens or hundreds of Gigabits per second (Gbps); however, a major inflection point occurred in 2016, when a 1.2 Terabits per second (Tbps) attack targeted Dyn, a managed DNS provider. This was an incredible and sudden escalation of scale, representing twice the power of any such attack previously recorded. For the first time, the DDoS attack’s potential for widespread, systemic disruption was demonstrated to the world.
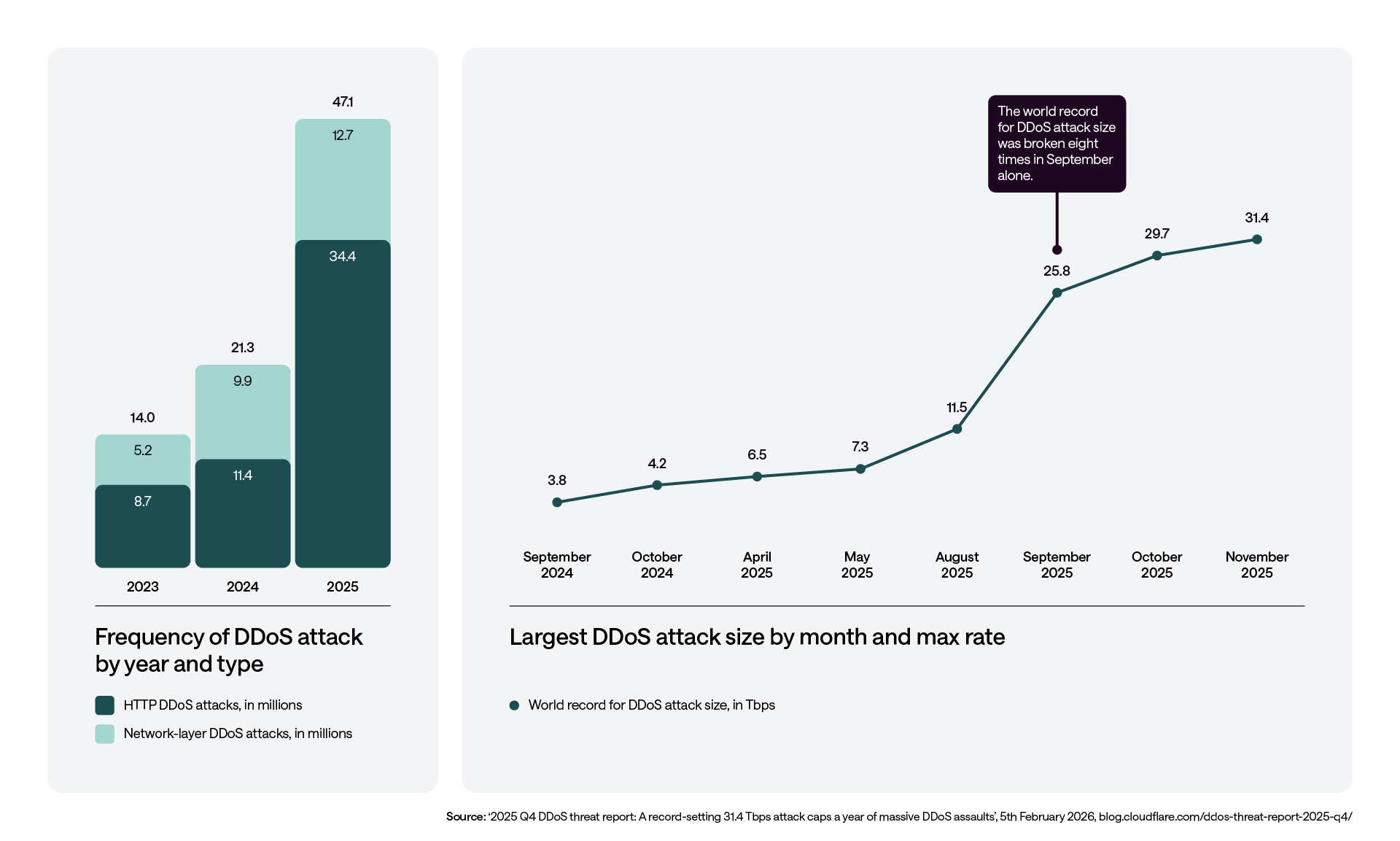
Since the Dyn attack, the scale and frequency of DDoS attacks have increased dramatically. Cloudflare’s report reveals an approximate 47 million incidents – compared to 21 million in 2024, and 14 million in 2023. Meanwhile, the largest recorded attack topped 31.4Tbps – a 2,516% increase from the 2016 Dyn attack that took down much of the USA’s internet services. This rapid – and accelerating – escalation highlights how the accessibility of modern attack infrastructure and automation have supercharged threat actors’ ability to use DDoS attacks to cause major disruption.
Who is perpetrating these attacks?
At a global level, DDoS attacks are conducted by a wide variety of threat actors, driven by a diverse range of motivations. At the lower-impact end of the scale, so-called ‘script kiddies’ and commoditised third-party DDoS-for-hire services are common. The most disruptive and sustained attacks, however, are typically carried out by organised criminal groups or hacktivist collectives.
Criminal groups frequently use DDoS attacks as part of wider extortion campaigns, either threatening or executing service disruption as a means to demand payment. Hacktivists, in contrast, are more commonly ideologically motivated, and may look to disrupt critical services as a way to draw attention to a perceived grievance or to sway public opinion – sometimes aligned to, or with the support of, nation states. The NCSC’s recent warning went as far as to highlight the increased activity of Russia-aligned hacktivist groups targeting critical infrastructure and local government systems in the UK, recommending that defences are strengthened in the face of an increasing amount of DDoS attacks in the sector.
Which businesses are a target?
While almost all organisations are potential targets, certain sectors face a disproportionately higher risk. Telecommunications, hosting, and online gaming providers are frequent targets due to the broad and immediate impact such disruption can have on their critical services – and, by extension, their customers.
In recent years, multi-terabit-per-second DDoS attacks have been directed at major cloud and platform providers such as Google, Amazon Web Services, and Microsoft. While these attacks were significant in scale, the majority were effectively mitigated through the use of highly advanced detection, automation, and globally distributed mitigation capabilities, highlighting both the severity of the threat and the effectiveness of modern, cloud-scale defences.
How will the threat grow with technology?
We can expect both the volume and sophistication of DDoS attacks to significantly increase over the coming years – above and beyond what we’re already seeing – driven, in part, by advances in automation and AI. Large-scale botnets are now readily available for the prospective attacker, and can be leveraged to launch highly effective attacks that are capable of overwhelming even well-resourced organisations through sheer volume.
At the same time, it’s increasingly common for attackers to adopt complex, multi-vector techniques designed to evade traditional flow-based detection controls by closely mimicking legitimate user behaviour. These novel attacks often rely on short, high-intensity bursts of traffic that last only minutes at a time, enabling them to bypass static thresholds while still causing rapid service disruption. It is also important to recognise that even comparatively simple volumetric DDoS attacks continue to be highly effective, and are frequently deployed as a distraction to mask more targeted intrusion or data exfiltration attempts elsewhere in the environment. As a result, it’s critical that organisations maintain robust defences and heightened awareness during such events.
How can firms protect themselves against this type of attack?
When considering DDoS risk, organisations need to distinguish between two separate layers of attack: volumetric attacks at Layers 3 and 4 (network and transport, respectively), and application-layer attacks at Layer 7.
When dealing with volumetric threats, it’s important to work closely with your internet service provider (ISP), as this typically provides access to the large-scale mitigation capabilities delivered by vendors such as Radware, Akamai, and Cloudflare. These cloud-based services will operate well beyond the limits of any defences found on-premises, and will often be integrated directly into your service offering – enabling attacks to be mitigated upstream, before they ever impact your local infrastructure.
Meanwhile, application-layer attacks require additional, more granular protections, such as a web application firewall (WAF), or web application and API protection (WAAP) platform. These controls are designed to detect techniques such as code injection and the abuse of application logic, applying behavioural analytics to distinguish legitimate users from malicious traffic and ensuring the continued availability of critical services.
Beyond these direct security controls, organisations need to build resilience into their environments. This includes auto-scaling applications and load balancers, as well as the deployment of services across multiple regions to minimise single points of failure. Finally, regardless of the solution deployed, it’s essential to regularly test these resilience measures and establish clear escalation paths with your service providers, to ensure a rapid, coordinated response when an attack occurs.



