Blog
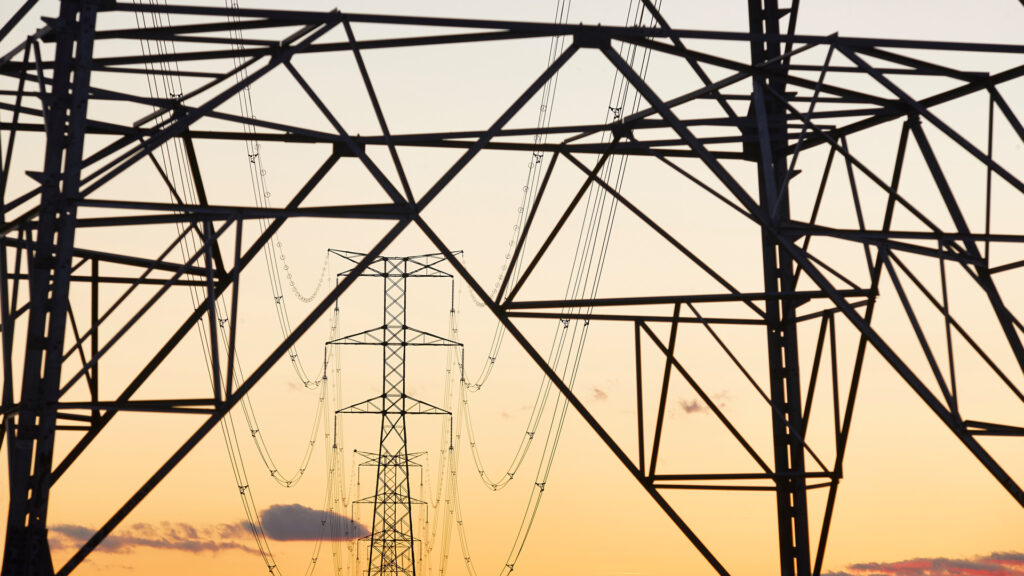
Deep Dive into the May 2023 Cyber Attack on Danish Energy Infrastructure
Danish energy infrastructure endured a sophisticated cyber attack, signifying a major escalation. This post analyzes the unprecedented assault, offering insights for cybersecurity professionals.
A Sophisticated Cyber Offensive: Unraveling the Layers
In May 2023, the Danish critical energy infrastructure faced a meticulously orchestrated cyber attack, marking a significant escalation in cyber warfare tactics. This blog post delves into the intricate details of this unprecedented assault, providing an in-depth analysis for cybersecurity professionals seeking to understand the intricacies of such sophisticated attacks. Thanks to SektorCERT for making their report public.
The Anatomy of the Attack
The Danish energy sector, encompassing 22 key companies, was targeted in a multi-faceted cyber operation. The attack’s complexity was not just in its execution but also in its strategic planning and the exploitation of specific vulnerabilities.
Exploitation Tactics:
- Zero-Day Exploits: The attackers leveraged undisclosed vulnerabilities, demonstrating advanced technical knowledge and resources.
- Spear Phishing and Social Engineering: These initial intrusion techniques were tailored to bypass standard security measures.
- Lateral Movement: Once inside the network, the attackers moved stealthily, escalating privileges and accessing critical systems.
Attack Vectors:
- Supply Chain Compromise: The attack potentially involved compromising third-party vendors, a tactic that has become increasingly prevalent in targeting large, well-defended networks.
- Network Propagation: The use of sophisticated malware and ransomware facilitated the spread across the network, crippling critical operational capabilities.
The Cyber Kill Chain Perspective
From a cyber kill chain viewpoint, the attack demonstrated a full spectrum execution:
- Reconnaissance: Gathering intelligence on the targets.
- Weaponization and Delivery: Crafting and deploying bespoke malware.
- Exploitation and Installation: Achieving initial foothold and securing persistence.
- Command and Control: Orchestrating the attack through a remote infrastructure.
- Action on Objectives: Achieving the intended disruptive outcomes.
Advanced Persistent Threats (APTs): A Likely Scenario
The scale, sophistication, and resource intensity of this attack suggest the involvement of an APT group. These groups, often state-sponsored, execute campaigns aimed at long-term espionage or disruption. The attack’s characteristics align with known APT modus operandi:
- Persistent Access: The attackers maintained long-term access to the network, indicating a high level of stealth and patience.
- Advanced Evasion Techniques: The use of complex obfuscation methods to avoid detection.
- Highly Specific Targeting: The focus on critical infrastructure entities hints at a strategic, possibly geopolitical, motive.
Detailed Attack Analysis
The Initial Threat: A Critical Vulnerability
The saga began on April 25, 2023, when Zyxel, a producer of widely used firewalls, announced a critical vulnerability (CVE-2023-28771) in their products. Rated 9.8 out of 10, this vulnerability was easy to exploit and had severe potential consequences. The affected firewalls, vital for protecting industrial control systems, were now a gateway for attackers to target Danish critical infrastructure.
The Calm Before the Storm: Warnings and Urgency
In response, SektorCERT, a cybersecurity group, alerted its members to patch their Zyxel firewalls. Despite this warning, many organizations either underestimated the risk, assumed their systems were up-to-date, or were unaware of the vulnerable devices in their networks.
The First Wave: Coordinated Attack on Critical Infrastructure
On May 11, a coordinated cyber-attack targeting 16 Danish energy companies unfolded. Utilizing the CVE-2023-28771 vulnerability, the attackers selectively hit vulnerable firewalls, compromising 11 companies immediately. This exploit allowed attackers to control the firewalls and potentially access the critical infrastructure behind them.
The Response: A Race Against Time
SektorCERT rapidly formed an incident response team, addressing multiple aspects such as identifying affected companies, contacting members, collaborating with suppliers, and informing authorities. Their swift action was crucial in managing the situation and preventing further damage.
The Aftermath: A Wake-Up Call on Cybersecurity Hygiene
This incident highlighted the importance of regular software updates and vulnerability management. Many affected members had either neglected updates or were unaware of their critical role in cybersecurity.
The Second Wave: New Threats and Continued Vigilance
On May 22, a second wave of attacks began, indicating that the attackers might have had access to previously unknown vulnerabilities. SektorCERT’s monitoring and rapid response played a pivotal role in mitigating these attacks, though the full extent and nature of the vulnerabilities were not immediately clear.
The Involvement of Advanced Persistent Threats (APT)
One alarming aspect of the May 24 attacks was the potential involvement of Sandworm, a well-known APT group. Indicators suggested that this sophisticated group might have been involved, highlighting the complexity and high stakes of the attacks.
While the report stops short of directly attributing the attack to a specific actor, the sophistication and nature of the operation suggest state-sponsored involvement. Attribution in such cases is complex, often obscured by layers of proxies and deceptive tactics.

Let OT and IT play together safely – and gain insight into production
IT is crucial for a company’s operations and the ability to gain insights intoLearn about OT Security Best Practices and how Cisco Cyber Vision can provide an overview of OT devices in operation and m…
Conclusion & Recommendations
Systemic Vulnerabilities
Denmark’s decentralized energy system, with many smaller operators, revealed a systemic vulnerability where a single exploit could have widespread consequences. This situation underscores the need for a societal focus on collective cybersecurity measures.
Visibility Across
SektorCERT’s cross-company monitoring was instrumental in detecting and responding to these simultaneous attacks. This approach is vital for early detection and coordinated response to multi-target cyber threats.
Constant Attacks
The incident reaffirms that Danish critical infrastructure is under continuous cyber threats, necessitating vigilant and proactive cybersecurity measures.
Cooperation
The effective collaboration between SektorCERT, its members, suppliers, and law enforcement was key to minimizing the impact of these attacks.
Recommendations
Below, we provide SektorCERT’s and some of our own advice for all companies operating critical infrastructure to implement specific measures, including:
- Exposure of Services: Limit exposure of services to the Internet.
- Update Procedures: Establish efficient processes for updating and patching systems.
- Contingency Planning: Develop and rehearse contingency plans for rapid response to breaches.
- Log Collection: Implement cross-sector log collection and analysis.
- Network Mapping: Ensure comprehensive mapping of all network inputs.
- Network Segmentation: Segment networks to contain potential breaches.
- Device Identification: Identify and monitor all network devices.
- Supplier Management: Establish clear agreements and cooperation with suppliers regarding cybersecurity.
- Emergency Procedures: Prepare for and manage extended periods of island operation.
- Vulnerability Scans: Regularly conduct vulnerability scans to validate the security status.
Final Thoughts
The cyber attacks on Danish critical infrastructure are a stark reminder of the evolving cybersecurity landscape. The lessons learned from this incident are not just for Denmark but for all nations and companies overseeing critical systems. Proactive measures, cross-sector collaboration, and continuous vigilance are vital to safeguarding our interconnected world from such sophisticated threats.
About the author

David Kasabji
Head of Threat Intelligence
David Kasabji is the Head of Threat Intelligence at the Conscia Group. He leads the development and delivery of actionable intelligence across cyber defense and managed security operations, translating complex threat activity into clear outcomes for different audiences — from SOC analysts and incident responders to executive stakeholders and external communications. His work spans end-to-end intelligence operations: collection and analysis of adversary activity, threat actor and campaign profiling, IOC and TTP development, and intelligence-driven guidance for detection, threat hunting, and security prioritization. David is also actively involved in Digital Forensics and Incident Response, supporting investigations and crisis situations with rapid triage, context, and strategic recommendations. A strong focus of his role is continuously improving how intelligence is operationalized through standardization and automation to ensure it is timely, relevant, and measurable.nd strategic crisis management during incidents.
Related