Blog
Staying in control: why digital sovereignty matters for European organisations
In an increasingly precarious international environment, digital sovereignty in Europe is only becoming more important. Organisations must learn to navigate a less predictable context, where reliance on American hyperscalers means data is not as ‘out of reach’ as previously thought. This article will outline what digital sovereignty is and why it matters so much for organisations.

Jump to:
- What is digital sovereignty?
- A changing global landscape for Europe’s digital infrastructure
- How Europe is responding to digital dependence
- A growing awareness of data control and availability
- A new discussion around digital sovereignty
- Rethinking risk in a less predictable world
- AI, data and the risk of lock-in
What is digital sovereignty?
Digital sovereignty is the ability of a country or region to control its own digital infrastructure, data, and technology rules, rather than relying on foreign powers or companies. It touches everything from where data is stored and who has legal access to it, to which standards govern cloud services, software platforms, and emerging technologies.
In recent years, digital sovereignty has become a more pressing issue in Europe. As governments, businesses, and public institutions grow increasingly dependent on cloud services and global tech platforms – many of them headquartered outside the EU – questions of control, resilience, and long-term autonomy have moved from abstract policy debates to concrete operational concerns.
A changing global landscape for Europe’s digital infrastructure
In February 2025, the US administration issued sanctions targeting the International Criminal Court, and Microsoft took action to disconnect the chief prosecutor’s email account, citing compliance with US sanctions. For many European organisations, this was seen as evidence that US sanctions compliance can, in certain circumstances, result in forced suspension of digital services.
The most significant risk now comes from extraterritorial US legislation such as the Cloud Act, which allows US authorities to access data stored by US‑headquartered companies worldwide.
In the context of around 70% of the EU market being operated by American hyperscalers when it comes to cloud servers, this has made the international situation around digital sovereignty increasingly precarious.
How Europe is responding to digital dependence
The EU has reacted by implementing the Cyber Resilience Act, and within Europe there are some examples of companies and regions taking measures to increase their digital sovereignty.
One example is the region of Schleswig-Holstein in Germany, which has spent ten years creating digital infrastructure without Microsoft, despite many commentators suggesting that it could not be done.
But this is not just the case in Germany. It reflects a broader European trend where several militaries and national authorities are moving away from US-controlled cloud services to secure their digital infrastructure.
A growing awareness of data control and availability
While the example from Schleswig‑Holstein is an unusual case, companies are becoming increasingly aware of where their data is kept. Many organisations have come to a realisation regarding data sovereignty: even though data is stored in the EU, it does not necessarily mean that it is out of reach for actors in other jurisdictions.
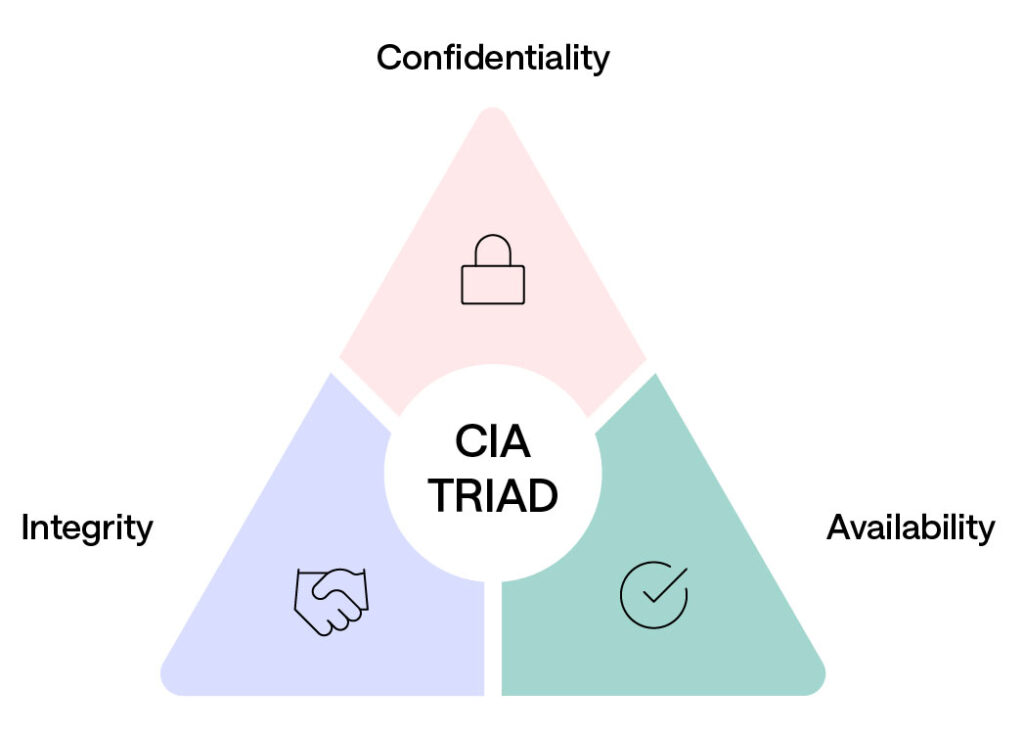
In cybersecurity, a common reference model is the CIA triad, which guides how data, systems and networks are protected through Confidentiality, Integrity and Availability. What is interesting is that until recently our clients at Conscia would usually focus on the C and the I, but now they are beginning to worry about A (availability) – ensuring that users have reliable access to data and systems.
This growing focus on availability is driving interest in European solutions. Organisations are beginning to question whether existing platforms can guarantee continued access in more unpredictable geopolitical conditions.
In practice, this is already affecting procurement. During tender processes, European customers are increasingly asking for data centres hosted in Europe and free from US jurisdictional influence. In some cases, this excludes a significant proportion of available solutions and forces organisations and providers alike to reassess which technologies can meet these tighter requirements.

Securing IaaS for Cegal
Cegal has taken a strategic step towards a more flexible, innovative IT day-to-day and chose Conscia as its IaaS partner along the way. Conscia’s data centre is located at Green Mountain, outside Stav…
A new discussion around digital sovereignty
What we are seeing is the beginning of a new discussion in Europe. Company leaders are increasingly asking whether they are comfortable being entirely reliant on US technology providers.
American vendors are deeply embedded in most organisations’ digital environments. However, this does not mean there are no choices. One option is to begin balancing your technology portfolio and taking a more deliberate approach to the use of hyperscalers.
There are alternative providers with roots in Europe and Japan, and while few organisations would advocate the kind of wholesale shift seen in Germany, simply asking these questions can have an important effect. It signals to large US providers that customers are reassessing their dependencies and expect greater flexibility in response.
Rethinking risk in a less predictable world
When organisations decide which technologies to adopt, risk assessments remain essential. These typically weigh the likelihood of an event against the potential consequences.
In the current climate, carrying out such assessments has become more difficult, but also more important. Companies are already used to applying this type of scrutiny to certain regions, such as assessing whether products from China might contain back doors that could expose sensitive data.
Recent sanctions cases demonstrate that service access can be disrupted when providers are required to comply with government decisions. This is also part of having a wider discussion about European digital sovereignty – not only beginning to balance your portfolio but assessing risk more intelligently at the same time.
AI, data and the risk of lock-in
Training-quality data has become a strategically critical resource in the development of AI capabilities. AI is therefore a focal point of the digital sovereignty discussion – not only when it comes to how companies train their data, but where that data is held.
AI depends on access to large volumes of data and sufficient processing power, yet many organisations underestimate how important it is to understand where their most valuable data resides. When data is held in the cloud, companies are effectively tied into their provider’s AI services. Moving that data elsewhere can incur significant egress fees – pricing models and technical dependencies can make later migration more complex and costly than initial adoption.
There is also limited flexibility once an organisation has committed to a particular AI platform. Switching providers, especially for training purposes, is often complex and expensive, increasing the risk of long‑term lock‑in.
This challenge is already visible for data‑rich organisations. Danish energy companies, for example, have vast amounts of data and clear opportunities to apply AI. The question is not whether to use AI, but where that data should live. Options may include running their own infrastructure or working with providers operating within the EU, both of which must also align with regulatory requirements across different jurisdictions.
If AI is the ‘new oil’, organisations need to ensure that they retain control over it, rather than giving it away by default.
In the second article in our digital sovereignty series, we move from theory to practice by re-examiningconversations around cloud, on-prem and hybrid models in an increasingly uncertain digital landscape. Read it here
About the author

Thomas Grønne
Director, Security Business, Conscia Danmark A/S
Thomas holds a Master’s degree from DTU and has more than 30 years of experience in IT security. He founded the IT security company RespektIT, which later merged with Credocom and was acquired by Conscia. Thomas is Director of Security at Conscia Denmark, where he communicates new trends and developments in IT security, strategic direction in the security area, and ensures that our customers understand the full complexity of the IT security landscape.
Related










