How mature is your organization’s security posture?
As your digital footprint increases, so does your cyber/attack surface. A look at the statistics reveals the harsh reality many organizations face. For example, a cyberattack happens every 39 seconds, companies are targeted by ransomware attacks every 14 seconds, and more than 90% of successful attacks against businesses originate from phishing. With cyber threats varying per company and industry vertical, there’s no one size fits all. Although cybersecurity is a must-have for today’s digital age, many companies struggle to identify vulnerabilities or understand what activities should be prioritized to improve their readiness.
Navigating what’s needed to address cyber threats is made easier with Conscia Maturity Assessment. With 5 levels, from basic to the most advanced, you are guided every step of the way by our certified experts.
The Maturity Assessment offers a structured approach for cybersecurity to become a business enabler against evolving cyber threats. Whether you want the Maturity Assessment to be a baseline, part of your regular ongoing security program, or even used to assess your supply chain partners and suppliers, Conscia puts you in control.
Why choose Conscia to perform a Maturity Assessment?
The Cybersecurity Maturity Assessment enables you to
- Gauge and remediate your organizational risk level
- Increase your organization’s security maturity with actionable recommendations
- Demonstrate progress and compliance all year long
- Elevate the importance of security across the business and your supply chain
- Encourage the right security behavior across the company
Solution Description
No matter which Industry Standard (e.g., CIS, NIST, NIS2) applies to your business, Conscia’s Maturity Assessment helps you improve cyber-resiliency and evolve your cybersecurity strategy.
Based on your preferred Industry Standard, our certified experts work with your subject matter experts across the organization to identify blind spots by looking at processes, people, and technology. We provide you with a detailed overview of current capabilities and give you an understanding of how to address the gaps in the form of a cybersecurity roadmap, complete with prioritized recommendations to improve your maturity.
The roadmap and recommendations let you focus on what matters most and secure the appropriate budget to optimize security investment. The Executive Dashboard presents a high-level summary of the critical findings helping CISOs easily communicate with the Board. All the details are available in drill down, enabling you to tailor relevant communication to meet different stakeholders’ needs across the business.
Relax, knowing that with Conscia, you have a partner you can trust.
Our cybersecurity solutions
Navigate through our cybersecurity solution framework below to read more about our solutions and services.
During an incident
Featured case studies

Caritas Trägergesellschaft Saarbrücken – Top-Level Security with Conscia

Vejle Municipality strengthens network security with enhanced visibility and proactive tools

Aarsleff’s managed services agreement provides assurance, security, and a future-proof network
Featured posts

Webinar: Unleash the Power of AI and Automation with Cisco Hypershield

Prisma Access Browser

Important Update for All Using Certificates for Single Sign-On
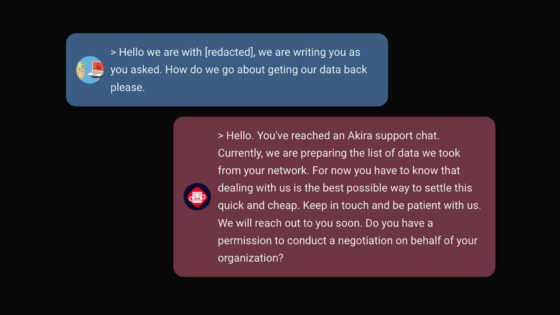
Hackers Turn Advisors: The $500K Irony of Akira Ransomware Gang’s Services

Microsoft LDAP vulnerabilities: Why cybersecurity teams need to act now
Offensive Security and Cyber Threat Intelligence: The Dynamic Duo Against Adversaries

Cisco Cyber Vision in Action: How to Secure Your OT Network

10 Secure online shopping tips for the Christmas season

From CAPTCHA to Compromise: Analysis of CAPTCHAclipper

Vulnerability Management

4 Things MDR/SOC Providers Don’t Like Talking About



